Illegal call centre operated luxury-style scam network targeting citizens in the US, UK, Canada and Australia; servers linked to crypto wallets traced offshore
Dateline: Gurugram | 25 November 2025
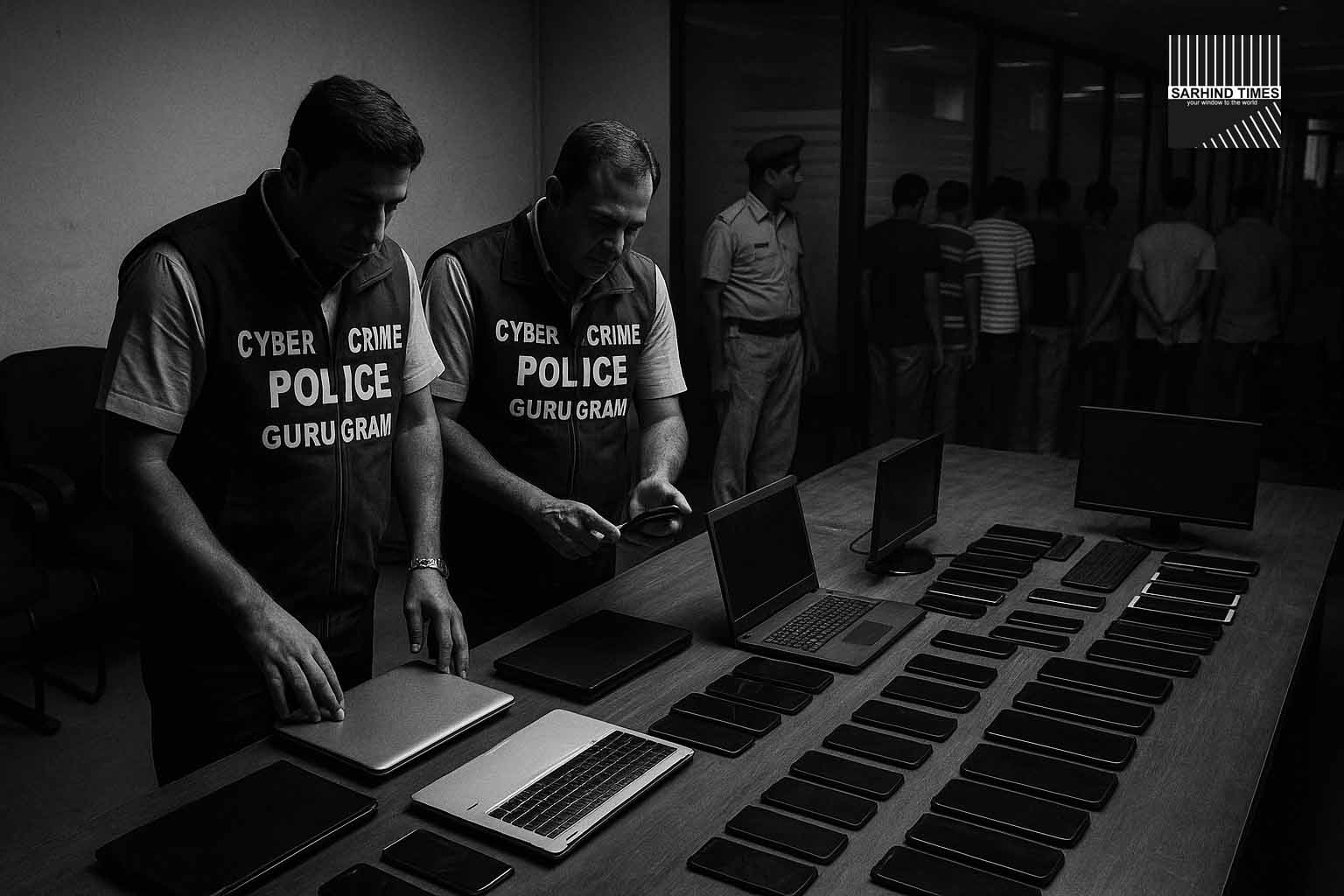
Summary: In one of the biggest cybercrime crackdowns of the year, Gurugram Police raided a multi-floor illegal call centre operating out of Udyog Vihar and arrested 47 individuals involved in an international tech-support and investment scam. Authorities recovered 312 computers, 98 mobile phones, 14 servers, ₹62 lakh in cash, and digital data containing personal information of over 1.2 million foreign nationals.
One of Gurugram’s Most Sophisticated Scam Networks Comes Down
Gurugram Police’s Cyber Crime team, working with the Special Task Force (STF) of Haryana, conducted a midnight operation that spanned nearly four hours and resulted in the arrest of 47 individuals operating a highly sophisticated international scam syndicate. The illegal call centre, located inside a corporate-style glass building in Udyog Vihar Phase-3, had been under secret surveillance for nearly three months.
What officers discovered inside shocked even seasoned cybercrime investigators. The floors resembled a polished corporate BPO, equipped with American-style cubicles, whiteboards with daily targets, CRM dashboards, VoIP calling equipment, and a dedicated crypto-transactions room. Every shift had a designated “floor manager,” “script trainer,” and “payment closer.”
Investigators said the operation was designed to mimic legitimate corporate processes so new employees would not immediately realise they were participating in a global fraud network. But the scripts, transaction patterns and victim communication logs revealed the true nature of the operation.
The Modus Operandi: A Three-Layered Fraud Network
The scam followed a three-step model commonly seen in transnational cybercrime operations—tech support impersonation, investment fraud and remote-access exploitation. Gurugram Police described three layers of operation:
- Layer 1: Lead Acquisition – The team used illegally purchased data sets containing phone numbers and email IDs of citizens in the US, UK, Canada and Australia. These data sets were found stored in encrypted folders recovered during the raid.
- Layer 2: Initial Pitch – Callers posed as representatives from global tech giants, banks or government departments, informing victims about security breaches, illegal account activity or pending compliance verifications.
- Layer 3: Payment Extraction – Victims were directed to install remote desktop applications, allowing the fraudsters to gain access to systems. Money was siphoned off through crypto wallets, prepaid cards and offshore shell companies.
Police say at least six different scam models were running simultaneously, including refund scams, antivirus renewal scams, courier package scams, IRS impersonation calls and Amazon impersonation frauds. Many victims lost anywhere between USD 500 and USD 25,000.
Digital Evidence: The 1.2 Million Victim Database
The most alarming discovery was a centralised server containing sensitive personal information of over 1.2 million foreign nationals. The database included:
- Full names
- Phone numbers
- Email addresses
- IP logs
- Payment attempt histories
- Past scam call outcomes
Cyber experts analysing the recovered devices say that the syndicate likely purchased this data from darknet vendors. The volume and quality of the data indicate a large-scale transnational operation linked to cybercrime networks based in Eastern Europe and parts of Southeast Asia.
Police are collaborating with international agencies to track the source of these stolen data sets and identify global partners involved in the operation.
Inside the Raid: A High-Pressure, Multi-Team Operation
The raid began shortly after 10:45 pm when a joint team of Cyber Police and STF officers entered the building following a well-coordinated infiltration plan. Officers were dressed in plain clothes to avoid alerting guards stationed at the entrance.
According to official accounts, the floors were fully active with night-shift employees engaged in live calls with foreign citizens. Computer screens showed remote-desktop sessions, live call scripts and crypto payment instructions.
One officer described the moment of entry: “It felt like a regular BPO at first glance. But as soon as we examined the screens and scripts, it was clear we had entered the nerve centre of a massive international fraud racket.”
Some employees attempted to escape through the back stairwell, but police teams had already secured all exits. Floor managers tried to destroy evidence by shutting down servers, but investigators were able to secure key hardware within minutes.
The Employees: Many Claimed They “Did Not Know”
A significant number of employees told police during questioning that they thought the operation was “legitimate customer support work.” Some had been hired recently through job ads on social media promising salaries of ₹28,000–₹55,000 per month plus incentives.
Police, however, are sceptical of these claims, noting that many cubicles displayed aggressive sales targets, dollar-based incentive charts and handwritten scam scripts.
“Even if they did not know on day one, the nature of calls and payments clearly showed they were scamming victims abroad,” an investigator stated.
Cash, Crypto, and Offshore Accounts: The Money Trail
The financial structure of the operation is unusually sophisticated. Officers recovered:
- ₹62 lakh in cash from drawers and manager cabins
- Signs of monthly cash payouts exceeding ₹1.8 crore
- Crypto wallet ledgers with 317 recent transactions
- Evidence of funds routed through Dubai and Singapore
- Digital receipts of prepaid gift cards used for laundering
Police cyber forensics teams are tracking wallet addresses to identify larger pockets of stolen funds. Several wallets appear linked to known darknet marketplaces.
VoIP Infrastructure and “Spoofing Rooms”
The building’s third floor contained a dedicated section where engineers manipulated VoIP signals to spoof international phone numbers. Victims would see the caller ID as the official helpline of a bank or tech company, making the scam appear legitimate.
The “spoofing room” had:
- High-speed servers specifically configured for VoIP tunneling
- Multiple SIM boxes supporting hundreds of outbound lines
- Custom-made software for caller ID masking
Police believe foreign experts may have helped set up this infrastructure.
Victims Speak: Losses, Panic and Emotional Distress
After the raid, multiple foreign victims reached out on social media expressing relief. One elderly US victim stated she lost USD 8,400 to the same scam pattern discovered in Gurugram. Another UK victim reported losing GBP 3,200 after being tricked into believing her bank account was compromised.
Police are preparing to send official alerts through Interpol and global law-enforcement networks to notify victims and assist in evidence sharing.
Legal Action: IPC, IT Act and International Collaboration
A formal FIR has been registered under:
- Sections 419/420 (cheating)
- 467/468/471 (forgery and impersonation)
- Sections of the IT Act relating to identity theft, online impersonation and data theft
- Sections relating to criminal conspiracy
Gurugram Police have also initiated communication with cybercrime units in the US, UK, Canada and Australia. Extradition requests may follow for key masterminds suspected to be operating from outside India.
What’s Next: Follow-Up Raids Likely
Senior officials confirm that this raid is only the beginning. The seized devices contain names of several other operators, including call centres in Delhi, Noida, Bengaluru and Hyderabad. Police expect to conduct further raids based on data recovered.
One senior officer said: “The network we found is large enough to indicate a multi-city syndicate. We are expanding our investigation footprint.”
The Gurugram Cybercrime Landscape: A Growing Challenge
Gurugram, with its corporate infrastructure and easy access to talent pools, has become a hotspot for illegal call centres masquerading as professional BPOs. In 2024 and 2025 alone, more than two dozen major crackdowns were conducted in the NCR region.
However, investigators say that the sophistication of the latest operation is unprecedented. Unlike earlier scams that relied on basic VoIP calling, this one integrated real-time dashboards, offshore banking and custom-coded call scripts designed for psychological manipulation.
Conclusion: A Significant Victory, but the War Continues
The arrest of 47 individuals and seizure of massive digital evidence marks a major success for Gurugram Police and the Haryana STF. Yet, experts warn that cybercrime networks are adaptive and resilient. With global victims, crypto payments and international infrastructure, such operations can re-emerge in new forms if enforcement does not intensify nationwide.
For now, the crackdown stands as a powerful message: Gurugram will not be allowed to become a safe haven for cross-border scam factories. The war against cybercrime has many battles ahead — but this one was a crucial win.


+ There are no comments
Add yours